
Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
APT40, also known as TEMP.Periscope, Leviathan, and many other aliases, is a Chinese cyber-espionage group attributed to the Chinese Ministry of State Security (MSS). Active since at least 2009, APT40 has been implicated in numerous high-profile cyber-espionage campaigns targeting a variety of sectors, particularly focusing on maritime, defense, aviation, and technology. The group’s activities are aligned with China’s strategic objectives, including the modernization of its military and expansion of its maritime influence.
APT40’s operations have been linked to the Hainan State Security Department (HSSD) of the MSS, a provincial arm of China’s primary civilian intelligence agency. This attribution is supported by multiple cybersecurity agencies and organizations, including the Cybersecurity and Infrastructure Security Agency (CISA), the Australian Cyber Security Centre (ACSC). These organizations have collectively identified the group’s Tactics, Techniques, and Procedures (TTPs) as consistent with those used by state-sponsored Chinese actors.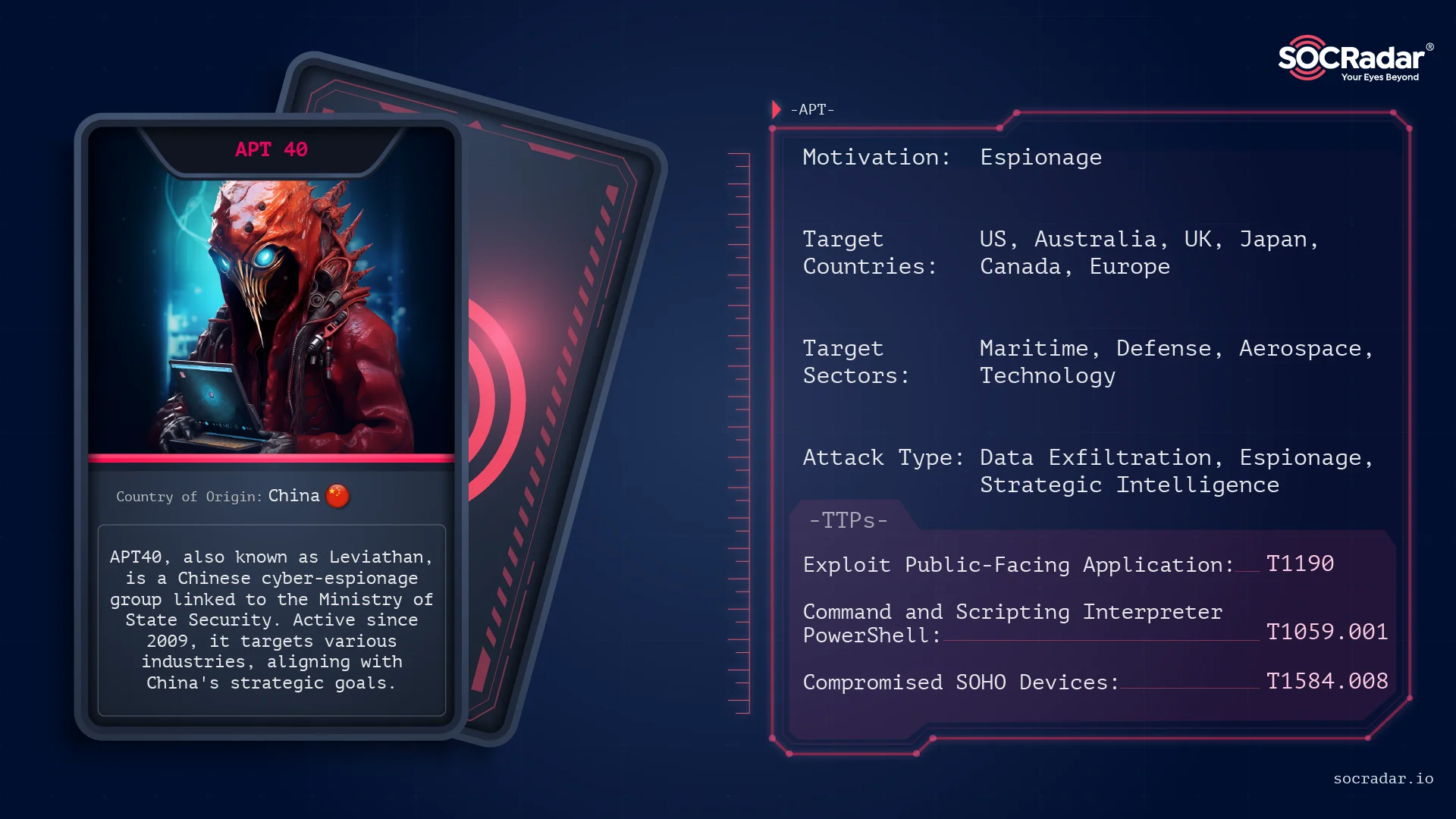
Threat Actor Card for APT40
As stated in the CISA advisory: On July 19, 2021, the U.S. Department of Justice (DOJ) unsealed an indictment against four APT40 cyber actors, revealing their illicit Computer Network Exploitation (CNE) activities conducted through the front company Hainan Xiandun Technology Development Company (Hainan Xiandun). Wu Shurong, an employee of Hainan Xiandun, collaborated with and executed orders from intelligence officers Ding Xiaoyang, Zhu Yunmin, and Cheng Qingmin of the Hainan State Security Department (HSSD) of the PRC Ministry of State Security (MSS).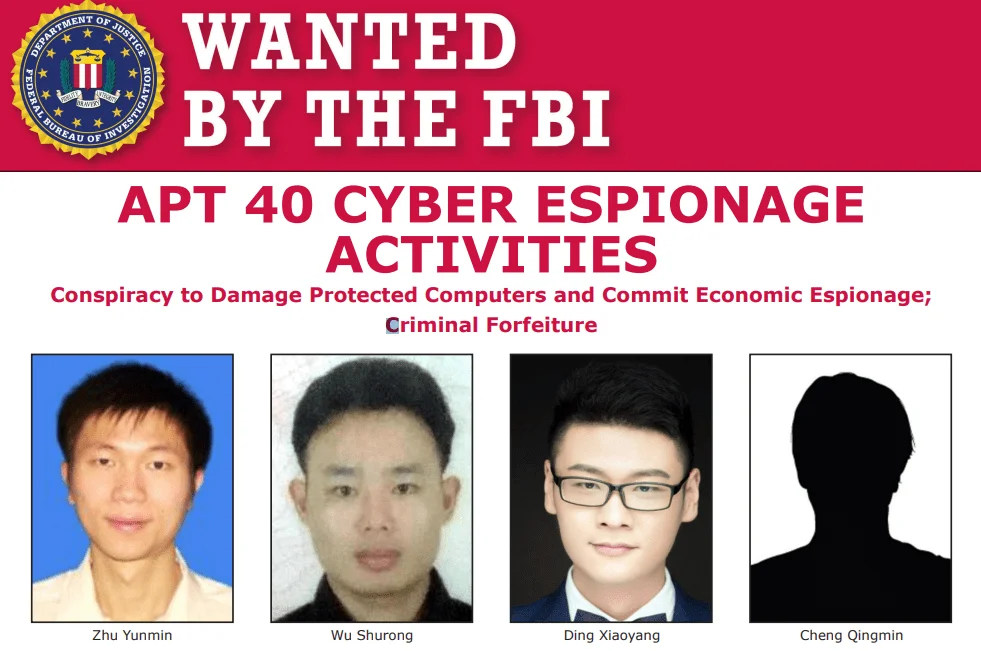
Wanted poster by the FBI (U.S. Department of Justice)
Wu’s CNE operations led to the theft of trade secrets, intellectual property, and other high-value information from companies and organizations in the United States and other countries, as well as from multiple foreign governments. These MSS-affiliated actors targeted victims across various industries, including academia, aerospace and aviation, biomedical, the defense industrial base, education, government, healthcare, manufacturing, maritime, research institutes, and transportation sectors such as rail and shipping.
APT40 employs a diverse array of TTPs to infiltrate, maintain persistence, and exfiltrate data from targeted networks.
According to ACSC, APT40 has the ability to swiftly adapt and utilize Proof-of-Concept (PoC) exploits for new vulnerabilities, deploying them immediately against target networks with the relevant infrastructure. The group consistently conducts reconnaissance on networks of interest, including those within the countries of the authoring agencies, to identify opportunities for compromise. This continuous reconnaissance allows APT40 to pinpoint vulnerable, end-of-life, or unmaintained devices on these networks and quickly deploy exploits. APT40 has successfully exploited vulnerabilities dating back to 2017.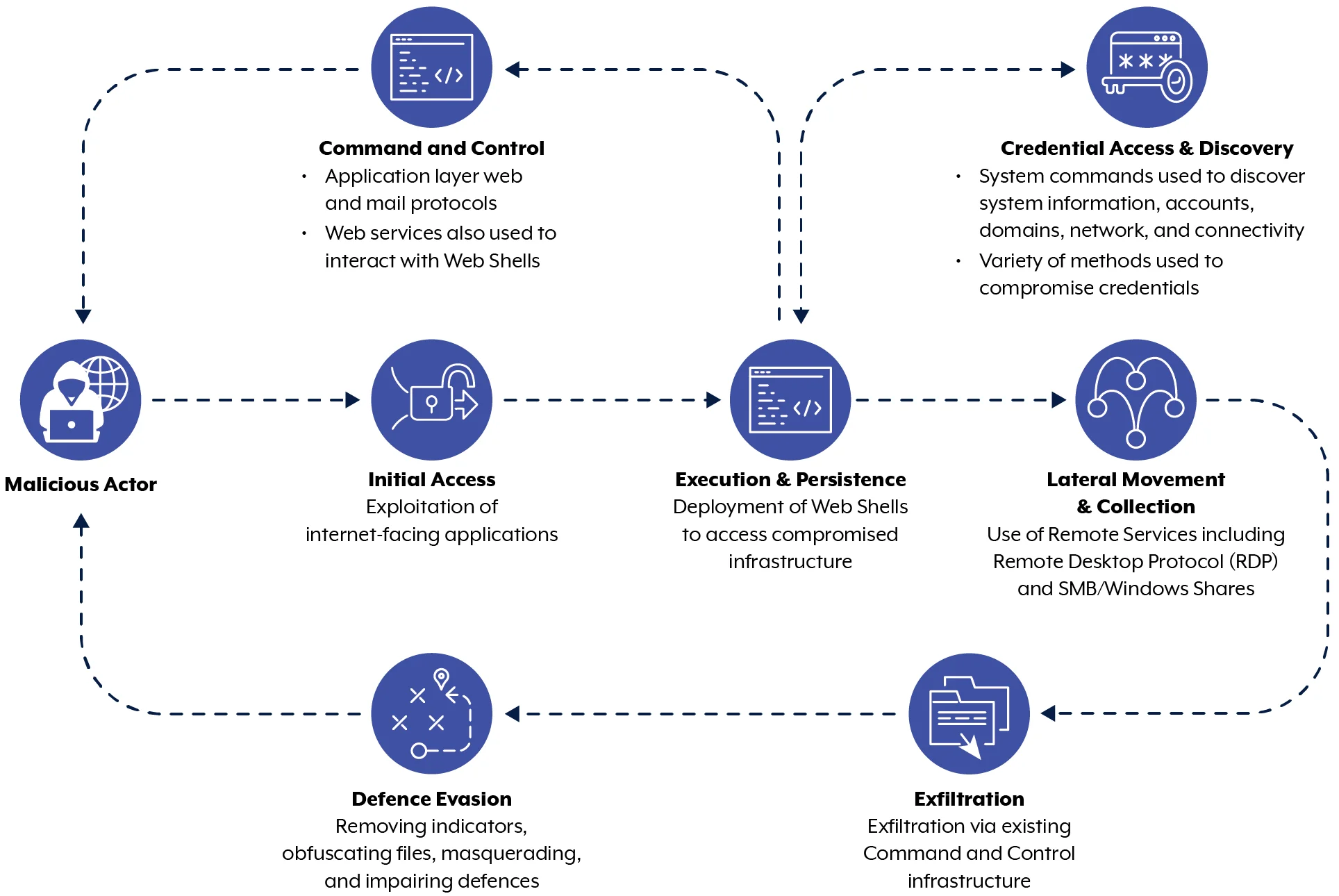
A flowchart of APT40’s modus operandi (ACSC)
Rapid Exploitation of New Vulnerabilities:
Continuous Reconnaissance:
Persistence Mechanisms:
Use of Compromised Infrastructure:
Command and Control (C2) Infrastructure:
As we mentioned above, APT40 has a well-documented history. As FireEye highlighted back in 2019, APT40 was targeting the maritime industry, reflecting China’s strategic interest in naval dominance and maritime trade routes. The group has targeted a variety of organizations, including research institutions, universities, and private companies involved in naval technology and maritime research. These attacks often aim to exfiltrate sensitive information that can be used to enhance China’s naval capabilities and inform its strategic decisions in disputed maritime regions, such as the South China Sea.
Key Incidents
APT40 has been involved in extensive cyber-espionage campaigns against the defense and aerospace sectors. The group’s operations are designed to gather intelligence on military technology, aviation systems, and satellite communications, providing the Chinese military with critical insights and technological advantages.
Key Incidents
The activities of APT40 pose significant threats to national security, economic stability, and technological advancement in the countries they target. The exfiltration of sensitive data can undermine competitive advantages, erode trust in public and private institutions, and lead to substantial financial losses. Additionally, the group’s focus on critical infrastructure and strategic sectors means that their activities have far-reaching implications for global security and geopolitical stability.
Organizations can take several steps to detect and mitigate the threat posed by APT40:
By implementing these measures, organizations can enhance their defenses against APT40 and other sophisticated cyber threats, reducing the risk of a successful attack and mitigating potential damage.
To counter the sophisticated cyber espionage tactics employed by the APT40 group, organizations are advised to adopt a proactive cybersecurity posture.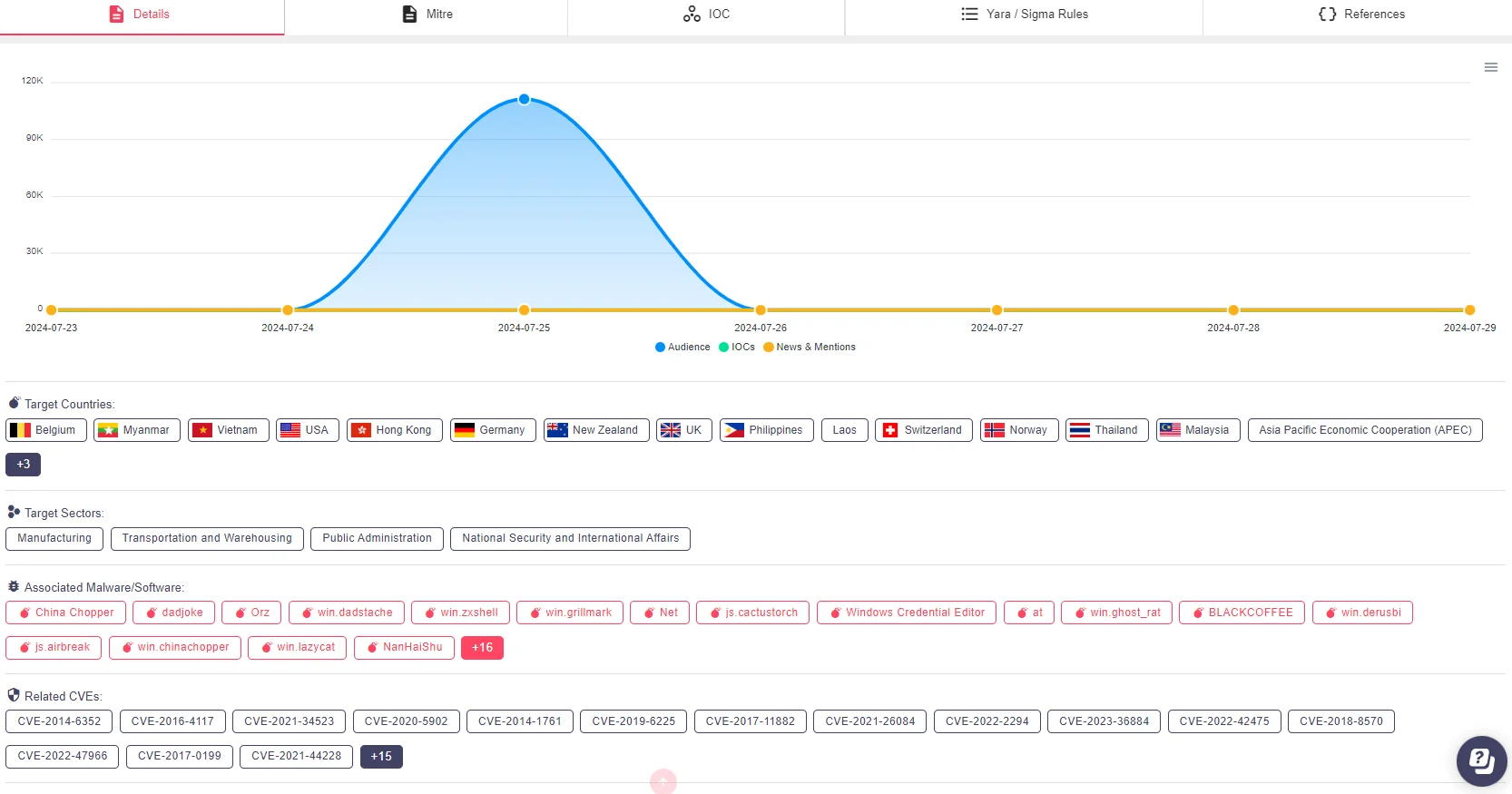
Threat actor page for APT40 in SOCRadar’s Platform, Threat Actor Intelligence
SOCRadar’s Extended Threat Intelligence represents a significant advancement over traditional threat intelligence platforms, incorporating advanced features that greatly enhance threat detection and visibility. This solution leverages powerful machine learning technologies to analyze vast amounts of threat data collected from a variety of open sources, social media platforms, and the dark web. By employing this comprehensive approach, SOCRadar’s XTI enables security teams to quickly identify and assess threats, providing them with proactive security measures.
APT40 remains a sophisticated and persistent threat actor, leveraging a wide range of techniques to achieve its espionage goals. Organizations, particularly those in targeted sectors such as maritime, defense, and aerospace, must stay vigilant and proactive in their cybersecurity efforts. By implementing robust security measures and staying informed about the latest threat intelligence, organizations can better protect themselves against the persistent and evolving threat posed by APT40.
Below are the TTPs provided by the CISA for APT40:
For more information, analysis, and Indicators of Compromise (IoCs) related to APT40, refer to resources from CISA and ACSC. Additionally, you can review our China & Russia Cybercrime report and access the SOCRadar Platform, which contains thousands of IoCs for APT40 and other related APT groups.
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
